April 1 passes, and so do the playful tricks and hoaxes that make April Fools' Day so memorable—leaving you double-checking every message. Yet, scammers keep working relentlessly.
Spring triggers a surge in cyberattacks. It's not due to negligence but because busy, distracted teams are flying through tasks. That's when deceptive scams slip through unnoticed, blending seamlessly into a hectic workday until damage is done.
Discover three prevalent scams currently targeting sharp, conscientious employees simply trying to make it through their day.
As you read, consider: Does my team consistently pause long enough to spot these scams?
Scam #1: Toll Road or Parking Fee Text Alerts
An employee receives a text:
"You owe $6.99 for an unpaid toll. Pay within 12 hours to avoid penalties."
The message cites a legitimate toll system—E-ZPass, SunPass, FasTrak—based on their location, with a small charge that seems harmless. Amid back-to-back meetings, they click the link, pay, and move on.
The problem? The payment link is fake.
The FBI reported over 60,000 complaints about fraudulent toll texts in 2024, with a 900% rise in 2025. Researchers uncovered more than 60,000 counterfeit domains mimicking state toll agencies, reflecting how lucrative this scam has become. Targets include people even from states without toll roads.
Why it succeeds: The low dollar amount seems risk-free and taps into everyday experiences like tolls or parking.
Protection tip: Authorized toll agencies never request instant payment via text. Encourage employees to avoid links in messages and always verify by visiting official websites or apps directly. Never reply to suspicious texts—even typing "STOP" confirms the number is active and invites further attacks.
When convenience tempts, strict process protects.
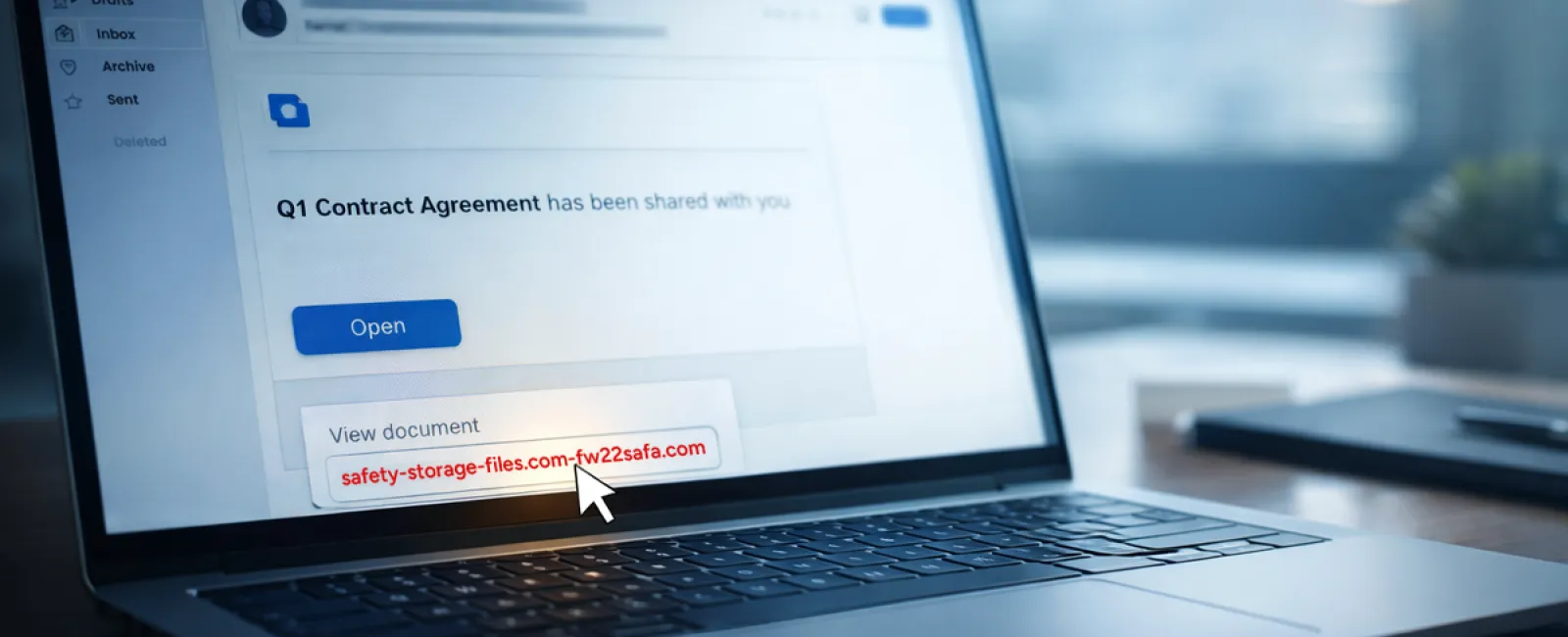
Scam #2: "Your File Is Ready" Email
This scam effortlessly mimics routine work.
An employee receives an email claiming a file was shared—typically a DocuSign contract, OneDrive spreadsheet, or Google Drive document.
The sender appears legitimate, and the email formatting matches usual notifications.
They click, log in when prompted, and unknowingly deliver their credentials to attackers.
With stolen credentials, hackers gain entry into your company's cloud environment.
Phishing via trusted platforms like Google Drive, DocuSign, Microsoft, and Salesforce surged 67% in 2025, according to KnowBe4's Threat Labs. Google Slides phishing alone rose over 200% within six months.
Employees are seven times likelier to click malicious links from OneDrive or SharePoint compared to random emails because the messages appear authentic.
Advanced scams use compromised accounts to send real notifications from legitimate servers, bypassing spam filters.
Protection tip: Train staff to avoid clicking unexpected shared file links in emails. Instead, log into platforms directly to verify files. Minimize risk by restricting external file sharing and enabling alerts for unusual login behavior—settings your IT team can configure quickly.
Consistent habits create strong defenses.
Scam #3: Impeccably Written Phishing Emails
Gone are the days when phishing emails had glaring mistakes.
A 2025 study revealed AI-crafted phishing emails achieve a 54% click rate—over four times higher than human-written scams at 12%. These emails mention actual company names, job titles, and workflows, scraped from LinkedIn and websites within seconds.
Attackers tailor scams to specific departments. HR may receive fake employee verification requests; finance employees encounter fraudulent vendor payment change emails. One test found 72% of employees engaged with vendor impersonation emails—90% higher than other phishing types. These messages are calm, professional, and urgent, blending into routine inbox traffic.
Protection tip: Verify any requests involving credentials, payments, or sensitive data through a second channel—call, chat, or in-person confirmation. Always hover over sender emails to confirm domains. Treat urgency in emails as a red flag.
Effective security doesn't rely on panic, but on vigilance.
The Core Lesson
Every scam thrives on familiarity, authority, timing, and the assumption that "this will only take a second."
The real vulnerability isn't careless employees—it's systems that expect perfect judgment under pressure.
If a rushed click can ruin your day, it's not a people problem—it's a flawed process.
And fortunately, process problems can be solved.
How We Support You
Business owners don't want cybersecurity to become another overwhelming task or the sole responsibility of one person.
They simply want assurance that their business is shielded quietly and effectively.
If you worry about your team's online safety—or know someone who should—we invite you to a straightforward discovery call.
During this call, we'll explore:
- Current cyber risks facing businesses like yours
- How everyday workflows create hidden vulnerabilities
- Simple strategies to reduce risk without disrupting productivity
No pressure. No scare tactics. Just honest conversations about keeping your business secure.
Click here or give us a call at (925) 766-4005 to schedule your free 15-Minute Discovery Call.
If this message isn't for you, please share it with someone who would benefit—sometimes knowing what to watch for is enough to transform a "would have clicked" into a "nice try."