Right now, millions are embracing Dry January—choosing to leave alcohol behind to feel healthier, boost their productivity, and stop procrastinating with vague plans like "I'll start Monday."
Your business faces its own version of Dry January—a list of tech habits that, like cocktails, are harmful rather than helpful.
You're familiar with these risky habits. Everyone knows they're inefficient or insecure, yet they're perpetuated because "it's fine" or "we're too busy."
But ignoring these issues comes at a cost.
Discover six damaging tech habits to eliminate immediately, plus practical alternatives to replace them.
Habit #1: Postponing Software Updates by Clicking "Remind Me Later"
This seemingly harmless button has caused more harm to small businesses than any hacker's attack.
We understand—no one wants their computer restarting during work hours. But updates don't just add new features; they often fix security vulnerabilities actively targeted by cybercriminals.
Delaying updates from days to weeks to months leaves your systems exposed, giving hackers easy access.
The infamous WannaCry ransomware attack, which affected businesses worldwide, exploited a flaw fixed by Microsoft months prior. Many victims had repeatedly clicked "remind me later."
The result? Billions lost across over 150 countries as operations ground to a halt.
Stop delaying: Schedule updates for the end of your workday or let your IT team apply them seamlessly in the background—no interruptions, no security risks.
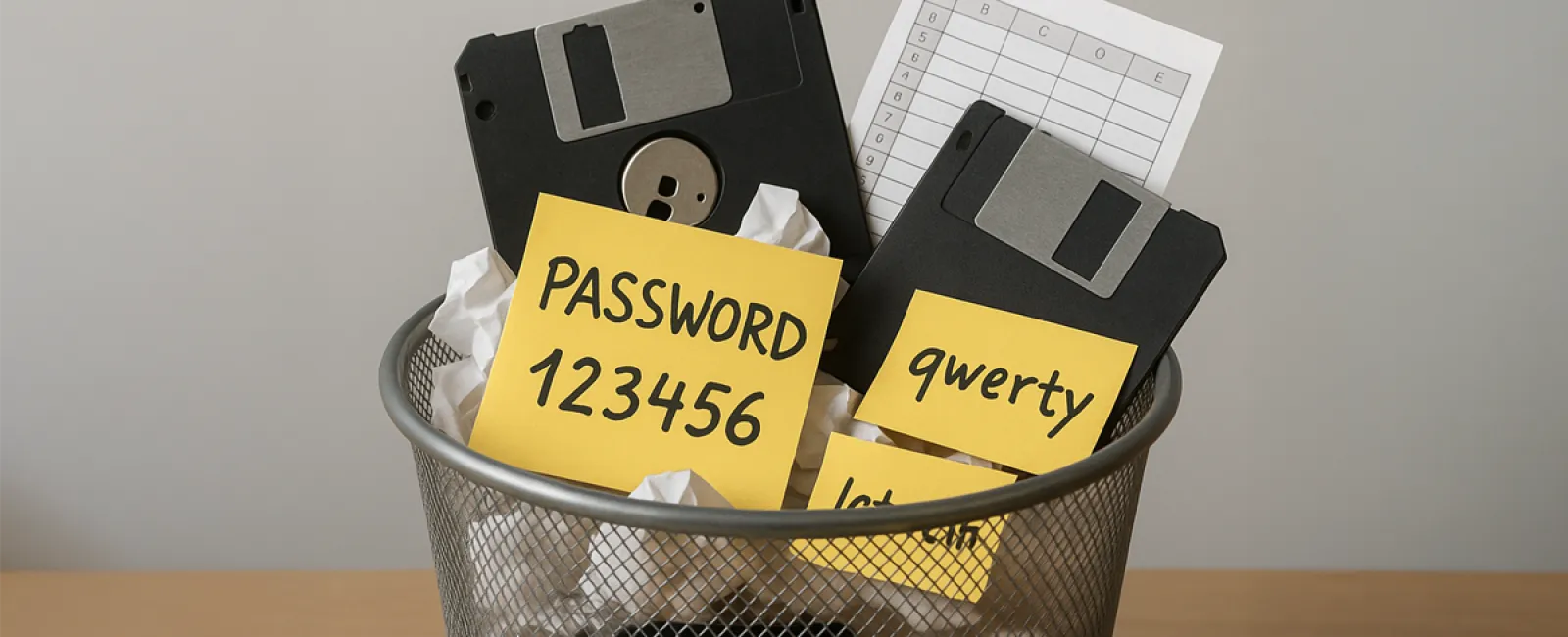
Habit #2: Reusing the Same Password Across Multiple Accounts
Everyone has a go-to password—something that meets security standards, feels strong, yet is easy to remember, and gets used everywhere: email, banking, Amazon, random forums.
The issue? Data breaches happen daily. Your password and email combo may already be exposed on hacker marketplaces.
Attackers use "credential stuffing" to try stolen credentials on various sites, effortlessly breaching accounts.
Your trusted password becomes a master key in the wrong hands.
Break the cycle: Employ a password manager like LastPass, 1Password, or Bitwarden. Remember one strong master password, and let the tool create and store unique, complex passwords securely for all your accounts—setup takes minutes, but gives you lasting security.
Habit #3: Sharing Passwords via Text, Email, or Chat
"Can you send me the login for that shared account?"
"Sure! It's admin@company.com and the password is Summer2024!"
Quick and convenient? Yes. Secure? Absolutely not.
Those messages linger forever—saved in inboxes, sent folders, backups, and are searchable. If anyone's email is compromised, hackers can easily find and misuse your shared credentials.
It's akin to mailing your house key on a postcard.
Secure sharing: Use password managers' encrypted sharing features. Recipients gain access without knowing the password, access can be revoked anytime, and no sensitive data lingers. If manual sharing is unavoidable, split credentials across different channels and immediately change passwords after.
Habit #4: Assigning Admin Rights to Everyone "Because It's Easier"
Maybe someone needed to install software or adjust settings once, and instead of setting precise permissions, they were given admin access.
Suddenly, a large portion of your team holds unrestricted admin rights.
Admin privileges allow installing apps, disabling security measures, altering crucial configurations, and deleting essential files. If their accounts are compromised, attackers inherit full control.
Ransomware thrives on admin accounts—more power means bigger damage, faster.
Granting everyone admin access is like handing out copies of your safe's keys because one person needed a stapler.
Stick to the principle of least privilege: Provide team members only the access necessary for their tasks. Though it might take extra effort upfront, it's a small price compared to the potential fallout from careless permissions.
Habit #5: Letting Temporary Workarounds Become Permanent Fixes
When something breaks, a quick workaround is found with a promise: "We'll fix it properly later."
Years later, that workaround is the standard process.
It might involve extra steps or require remembering hacks, yet since it "works," it gets left alone.
This accumulates lost productivity, and worse, creates fragile systems prone to failure when environments or personnel change.
Take action: List all current workarounds your team relies on. Instead of struggling alone to fix these, partner with experts who can implement permanent, effective solutions that save time and reduce frustration.
Habit #6: Relying on a Complex Spreadsheet to Run Critical Business Functions
You know the one: a labyrinthine Excel workbook with multiple tabs, complicated formulas, and only a handful of people who know how it works—sometimes none who remain with the company.
What happens if this file gets corrupted or the expert leaves?
This spreadsheet is a hidden single point of failure.
Spreadsheets lack proper audit trails, scale poorly, and often aren't backed up correctly. Building essential operations on such fragile foundations is risky.
Upgrade your tools: Document the business processes the spreadsheet supports and migrate to dedicated software—CRMs for customer management, inventory tools, scheduling apps. These platforms offer backups, user permissions, audit logs, and don't depend on individual knowledge. Remember, spreadsheets are great tools but poor platforms for critical business systems.
Why These Dangerous Habits Persist
You're not unaware of these pitfalls; you're overwhelmed.
Bad tech habits endure because:
- Risks remain unseen until disaster strikes—with repeated password use, everything seems fine until it isn't, and then it's too late.
- Proper methods feel slower initially—setting up password managers or adjusting permissions seems time-consuming compared to shortcuts, until the consequences of breaches prove devastating.
- When everyone else does it too, insecure behaviors feel normal, hiding the risks in plain sight.
Just like Dry January forces people to confront their drinking habits, breaking these tech habits requires awareness and environment change.
How to Finally Break These Habits With Ease
Willpower on its own rarely works; changing your environment is key.
Successful businesses make secure behavior effortless by:
- Rolling out password managers company-wide to eliminate insecure credential sharing.
- Automating software updates to remove "remind me later" temptations.
- Centralizing permission management to prevent unnecessary admin access.
- Replacing unreliable workarounds with solid, documented solutions.
- Transitioning critical spreadsheets to proper software with backups and access controls.
They design systems where the right choices become the easiest choices—leaving bad habits behind.
This is what a proactive IT partner offers: not just advice but meaningful system changes that set your business up for long-term success.
Ready to Break Free from Costly Tech Habits Holding Your Business Back?
Schedule your Bad Habit Audit today.
In just 15 minutes, we'll analyze your business challenges and provide a clear, actionable plan to resolve them for good.
No criticism. No confusing jargon. Just a pathway to a safer, faster, and more profitable 2026.
Click here or give us a call at (925) 766-4005 to book your 15-Minute Discovery Call.
Some habits deserve to be dropped cold turkey—and there's no better season than January to start.